Trending Now
DON'T MISS
Workout Routine for Big Forearms and a Crushing Grip
The model is talking about booking her latest gig, modeling WordPress underwear in the brand latest Perfectly Fit campaign, which was shot by Lachian...
LIFESTYLE NEWS
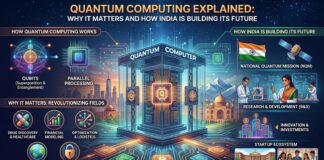
Quantum Computing Explained: Why It Matters and How India Is Building...
Introduction: The Next Big Leap in TechnologyWhat Is Quantum Computing in Simple Terms?Why Quantum Computing Matters1. Drug Discovery and Healthcare2. Financial Modeling3. Supply Chain...
Android’s “Tap to Share”: A Step Toward Frictionless Connectivity
The Race for Seamless SharingThe Problem: Friction in Everyday SharingThe Shift: What “Tap to Share” BringsComparing Ecosystems: Android vs iPhone ExperienceBusiness Perspective: Why This...
HOUSE DESIGN
TECH AND GADGETS
How to enable Native SSH client in Windows 10
Most awaited feature for developers is now on Windows 10. Yes! now you dont need any 3rd party ssh client on your windows developer...
MAKE IT MODERN
LATEST REVIEWS
Controversy Erupts in Maharashtra’s Beed as Teachers’ Intimate Videos Go Viral
In a shocking turn of events, a scandal has rocked the educational landscape of Maharashtra's Beed, leaving the community in disbelief. Videos allegedly depicting...
PERFORMANCE TRAINING
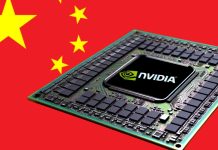
NVIDIA, AI Chips, and China: What’s Going On?
What Are AI Chips, Anyway?Why Is This About China?Why Would the U.S. Block Chip Sales?What Did NVIDIA’s CEO Say?How Does This Affect Business and...
When YouTube Broke: What Happened When the World’s Video Platform Stopped Working
One moment you're browsing funny clips or tutorials, the next: blank screen, “error,” or videos that simply won’t load. That’s what millions of YouTube...
Understanding Crypters: How They Work and How to Protect Against Them
In the intricate world of cybersecurity, malicious actors continually innovate to bypass detection systems and exploit vulnerabilities. One tool frequently used by these attackers...
Odoo’s Growth in the Middle East: A New Era for Businesses
Embracing Change in BusinessWhat is Odoo?Why is Odoo Popular in the Middle East?How Odoo Helps Different IndustriesReal-Life Example: Zolute's RoleBenefits of Using OdooConclusion: A...
How Elon Musk Built the World’s Largest AI Computing System in Just 16 Months
The Big Leap in Artificial IntelligenceThe Vision Behind xAIThe Engineering Feat: Building the World’s Largest AI SystemWhy Musk’s AI System Is RevolutionaryChallenges Along the...
HOLIDAY RECIPES
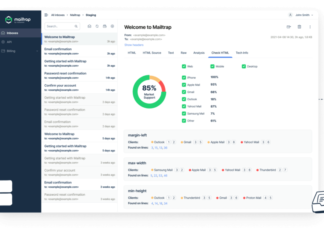
Test Email with this sandbox tool
Are you using your Gmail or some cPanel mail service to test send mail? As a developer you may require to test send mail...